On a recent Windows 7 deployment, I wanted to patch the base image during the Build and Capture task sequence in MDT 2013. I decided to reach out to the internet to download all the latest available updates, but quickly found that the client’s internet proxy was preventing the connection to the MS Update site. Automation is key during any task sequence, so I needed to find a way to import the necessary proxy settings without manual intervention so that my reference machine could download and install patches.
There are several ways to can accomplish this:
- Registry – You can directly add the required registry keys during the task sequence (import a .REG file or add each key individually). The registry path is:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings]
and the minimum set of keys needed are:
“ProxyEnable”=dword:00000001
“ProxyServer”=”10.10.10.1:8080” (replace with appropriate server and port number)
Depending on the configuration of the proxy, other registry keys might be required as well. The “ProxyOverride” key comes to mind in case the MS Update site should bypass the proxy.
- NETSH – You can leverage NETSH commands during the task sequence to set the proxy as needed with the following command:
netsh winhttp set proxy 10.10.10.1:8080 (replace with appropriate server and port number)
and the proxy can be reset following patch installation by running:
netsh winhttp reset proxy
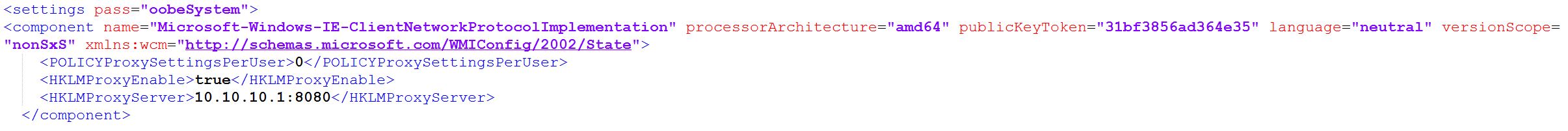
- Unattend.xml – You can update the Unattend.xml file used during OS installation to directly apply the desired proxy settings. In the “oobeSystem” pass, we can add a component section for “Microsoft-Windows-IE-ClientNetworkProtocolImplementation” and include the appropriate values for the proxy:
<POLICYProxySettingsPerUser>0</POLICYProxySettingsPerUser>
<HKLMProxyEnable>true</HKLMProxyEnable>
<HKLMProxyServer>10.10.10.1:8080</HKLMProxyServer>
The “HKLMProxyOverride” value can be added as well in case the proxy should be bypassed for certain configurations. One thing to keep in mind with this method is that the proxy settings are configured for the machine and that the proxy configuration page in Internet Options will be grayed out. Should more granular control of the proxy be required on a per-user basis, then either of the first two options above are preferred.
I tested all three methods with success and found that my reference machine was able to connect to the internet and download all of the available patches automatically.
One important caveat, however, is that these methods only work with an unauthenticated proxy. The MDT task sequence runs with the local administrator account of the machine and will therefore be unable to validate credentials if domain authentication is required. In this scenario, leveraging a local WSUS server would be preferred, as the proxy shouldn’t interfere with connecting to local resources.